
Wanna know a secret? Well if I were to tell you the secret on this webpage, it won’t be a secret any more as anyone can read it.
So how can I tell you the secret?
Activity 1
Discuss how you could share a secret with someone:
- In person
- Without meeting in person
For each situation, how can you be sure that the secret won’t be discovered by anyone else?
Caesar Cipher
People have wanted to share secrets for thousands of years without them being discovered by anyone other than the intended recipient. For example, in a battle where two armies might want to fight their common enemy, one army might want to join with the other at a particular location and time:
“WE ATTACK THE ENEMY AT DAWN FROM THE EAST”
Typically a messenger would travel with the note between the two armies. If that messenger is spotted and intercepted by the enemy, they could read the note and discover the plan. A way to secure the message in case the message IS intercepted, would be to scramble the text into a form that when read doesn’t make sense:
“ZH DWWDFN WKH HQHPB DW GDZQ IURP WKH HDVW”
The above seemingly nonsensical text is actually our original message but with each letter replaced by a letter 3 positions later in the alphabet.
Hence W becomes (X)(Y)Z and E becomes (F)(G)H.
The Y in enemy becomes B, because when we reach the end of the alphabet, we start again at the beginnning, hence Y becomes (Z)(A)B
We can decode the original message by reversing the process, so that each letter in the scrambled text is replaced with a letter exactly 3 positions earlier in the alphabet.
This simple idea, taking a plain text message and scrambling it into a form called cipher text that cannot be read unless a key piece of information is known, is the basis of encryption. In this case, the key piece of information (literally called a key) is how many letters in the alphabet we should shift each character in the message. This method was used by Roman Emperor Julius Caesar and hence is called the Caesar Cipher.
Because the same key used to encrypt the message is used to decrypt the message, we call this method symmetric encryption.
Activity 2
Assuming it has been encrypted using the Caesar cipher, decrypt the following text on paper showing your method:
- HEC SJJ (Key=4)
- EHQWOHB SULRUB (Key= 3)
- OERNX GVZR (Key =13)
Issues
Whilst the Caesar cipher is better than nothing, it is incredibly easy to crack. You simply need to try every different key value from 1 to 25 until you get a message that makes sense. This is called brute force hacking as there is no cleverness to it, you just throw time at the problem and you will eventually get to the solution. You could even write a computer program to do it for you in fractions of a second (demo).
Fortunately there are many ways that data can be encrypted, and most modern ones would take too long to decrypt using brute force, even using a computer.
Frequency Analysis
Another potential way that cipher text could be cracked is through analysis of the characters in the encrypted text. Some letters occur more frequently than others. In English, the most common letter used in written text is the letter “e”. The letter “z” would be relatively rare in English, but more common in Polish. If we know the language that an encrypted text is written in, we can concentrate our efforts on the more common letters we would expect to see in the plain text.
Even knowledge of facts such as the most common starting letter for a word in English (it’s “A“) could be helpful in trying to crack the code.
Using statistics, and lots of sample encrypted messages, it is sometimes possible to crack even very complex encryption methods. This was the case in World War 2 when codebreakers managed to crack the Engima code used by Germany (as depicted in the movie, the Imitation Game).
Vernam Cipher
At the other end of the spectrum from the Caesar Cipher, the Vernam Cipher should be impossible to decrypt using brute force methods. In this method of encryption, every symbol of the original data is XOR’ed with a unique value in something called a pad. The pad length is the same as the length of the data to be encrypted. Every value in the pad should be random and the pad should only ever be used once and then destroyed. The resulting value from the XOR represents the encrypted data.
The data can be text, but does not have to be, so anything can be encrypted.
In the example below involving a message of length 1, the character “A” (decimal 65 as ASCII) is XOR’ed with a pad value of “/” (decimal 47). The resulting encrypted value is decimal 110 which could be displayed as the character “z“
| 128 | 64 | 32 | 16 | 8 | 4 | 2 | 1 | |
| Data | 0 | 1 | 0 | 0 | 0 | 0 | 0 | 1 |
| Pad | 0 | 0 | 1 | 0 | 1 | 1 | 1 | 1 |
| XOR | 0 | 1 | 1 | 0 | 1 | 1 | 1 | 0 |
A longer message would need a longer pad of equal length, with each value being unique and random.
To retrieve the original data, we XOR the encrypted data with the same pad.
| 128 | 64 | 32 | 16 | 8 | 4 | 2 | 1 | |
| Data | 0 | 1 | 0 | 0 | 0 | 0 | 0 | 1 |
| Pad | 0 | 0 | 1 | 0 | 1 | 1 | 1 | 1 |
| XOR | 0 | 1 | 1 | 0 | 1 | 1 | 1 | 0 |
| 2nd XOR | 0 | 1 | 0 | 0 | 0 | 0 | 0 | 1 |
Activity 3
Encrypt the following using the Vernam Cipher with the given pads
- Text=CPU, Pad=$1c
- Text = HELLO, Pad=b1h6d
- Text=COMPUTER, Pad= !ag1?v2k
Issues
The issue with the Vernam Cipher is generating the pad. Every value in the pad should be completely random so that no frequency analysis at all can be done. In practice it is quite hard for a computer to generate a genuinely random number. They usually are pseudo-random, meaning that they appear to be random but there is an apparent pattern, and if you know the algorithm used to generate the random number, it is possible to guess what the next random number in the sequence will be. To be genuinely random, some unpredictable real world quantity is used to generate the pad values, for example:
- atmospheric noise
- decay of a radioactive source
- mouse movement
- the state of subatomic particles
Symmetric Encryption
As we said earlier, the Caesar Cipher is an example of symmetric encryption. This means that the same key is used to encrypt and decrypt data. To ensure secrecy we need to keep the key safe and private. Hence it is called a private key.
The problem with using symmetric encryption over a network is that the key has to be shared with the recipient. So if you are sending the message encrypted, and the key along with it, anyone intercepting both can decrypt and therefore read the message and we are back where we started! We need to keep the key private in order for the data to be secure.
Symmetric encryption can still be useful in certain situations. If you are not transmitting the key, you can still keep the encrypted data secure. An example would be encrypting the contents of your hard disk, which is good practice when doing a back up. If someone got hold of the back up files, they could read all your data. However if you encrypted the data using a private key, noone could read the files unless they knew the private key value.
Asymmetric Encryption
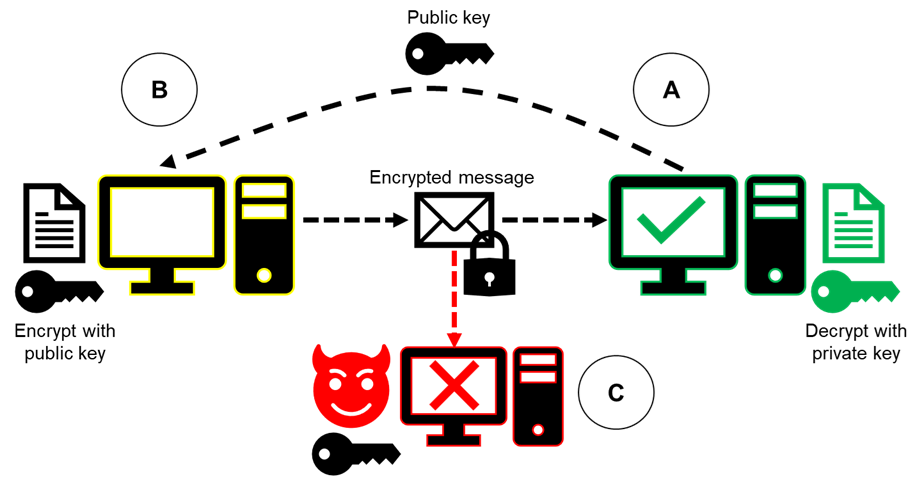
To overcome the issue with keeping private keys private, a solution involves a related pair of keys to encrypt and decrypt data. The pair of keys consists of a private key, and a public key. The private key is never transmitted over a network and is therefore secure. The public key can be sent over a network and should be used by the recipient to encrypt any data being sent back to the owner of the keys.
The owner of the keys can decrypt the data using the private key. Since this never gets transmitted anywhere we can be sure that the communication was secure.
Activity 4
Copy the diagram into your book, making sure to colour the private and public keys differently (back to back if time and a partner available)
Digital Signatures
There is a possibility that the hacker at computer C, who has access to the public key could send encrypted data to computer A, who could then decrypt it. What if they pretended to be computer B and sent a fake document to computer A?
To guard against such issues, a digital signature can be sent with any data being transmitted. The digital signature allows the recipient to verify that “B sent this data, and it has not been altered“.
The process works by producing a checksum (sometimes called a hash total) of the data to be sent. This involves just adding up every single byte of the data. e.g. a small binary file consisting of the values:
3, 7, 9, 2
… would produce a checksum of 21.
If the data is altered when being sent, a recalculated checksum will produce a different number, and we will know that the data has changed.
So in this case, Computer B creates a digital signature by first producing a checksum of the data it is sending to Computer A. It encrypts this checksum using its private key. This checksum encrypted with computer B’s private key is computer B’s digital signature.
It then encrypts both the data to be sent and the digital signature using Computer A’s public key and sends it. Computer A will also need a copy of Computer B’s public key.
Computer A can now decrypt the data from Computer B using its own private key. It can recalculate the checksum from the data that was sent. Using B’s public key, it can decrypt the digital signature from B which recovers the original checksum. If the two checksums match we know that B sent the data, and it has not been altered.
Activity 5
Create a new annotated diagram, based on the one from Activity 4, that shows the process of key exchange and encryption for the digital signature process. Use different colours or symbols for A and B’s different private and public keys
Digital Certificates
A digital signature confirms that a particular person sent some data and it was not altered. It confirms the trustworthiness of the data. A digital certificate is something that confirms the trustworthiness of the sender.
Digital certificates are issued by official Certificate Authorities (CAs). The most common one is a company called Verisign, but there are others such as Digicert and Thawte. You must pay for the certificate and its renewal. Digital certificates contain:
- a serial number
- name of the holder
- expiry date
- copy of the public key
- the digital signature of the Certificate Authority
A holder of a digital certificate enables them to use the Public Key Infrastructure or PKI. This is the collection of systems that allow secure communication over the Internet, for example the HTTPS: protocol.
Activity 6
Answer the following exam questions:
- Explain how digital signatures ensure the integrity of data communications (4 marks)
- Paper 1 June 2018, Q8d
Knowledge Check
- Why would you want to scramble a message?
- What is the issue with a Caesar cipher?
- How can frequency analysis help to crack an encryption scheme?
- Which letter from A-Z would you expect to have the most shelf space in a school library in England?
- Is the Vernam Cipher symmetric or asymmetric?
- What could compromise the Vernam Cipher?
- What is a flaw with symmetric encryption?
- Where can symmetric encryption encryption still be useful?
- How does asymmetric encryption solve symmetric encryption’s issue?
- What is a down side of asymmetric encryption?
- How do digital signatures aid secure communications?
- What is a digital certificate used for?
- Why could secure communication potentially be a bad thing?